Published: Nov 23, 2020 by Isaac Johnson
I created an AliCloud account a long time back to test their initial K8s offering but never figured out the UI. I went back to see what they had to offer by way of container registries. From what I can tell, the standard/single user Container Registry is free for now, which is my favourite price. In this post we’ll dive into China’s premier cloud provider and see how well it works.
Create an account
Create an account if you haven’t already.
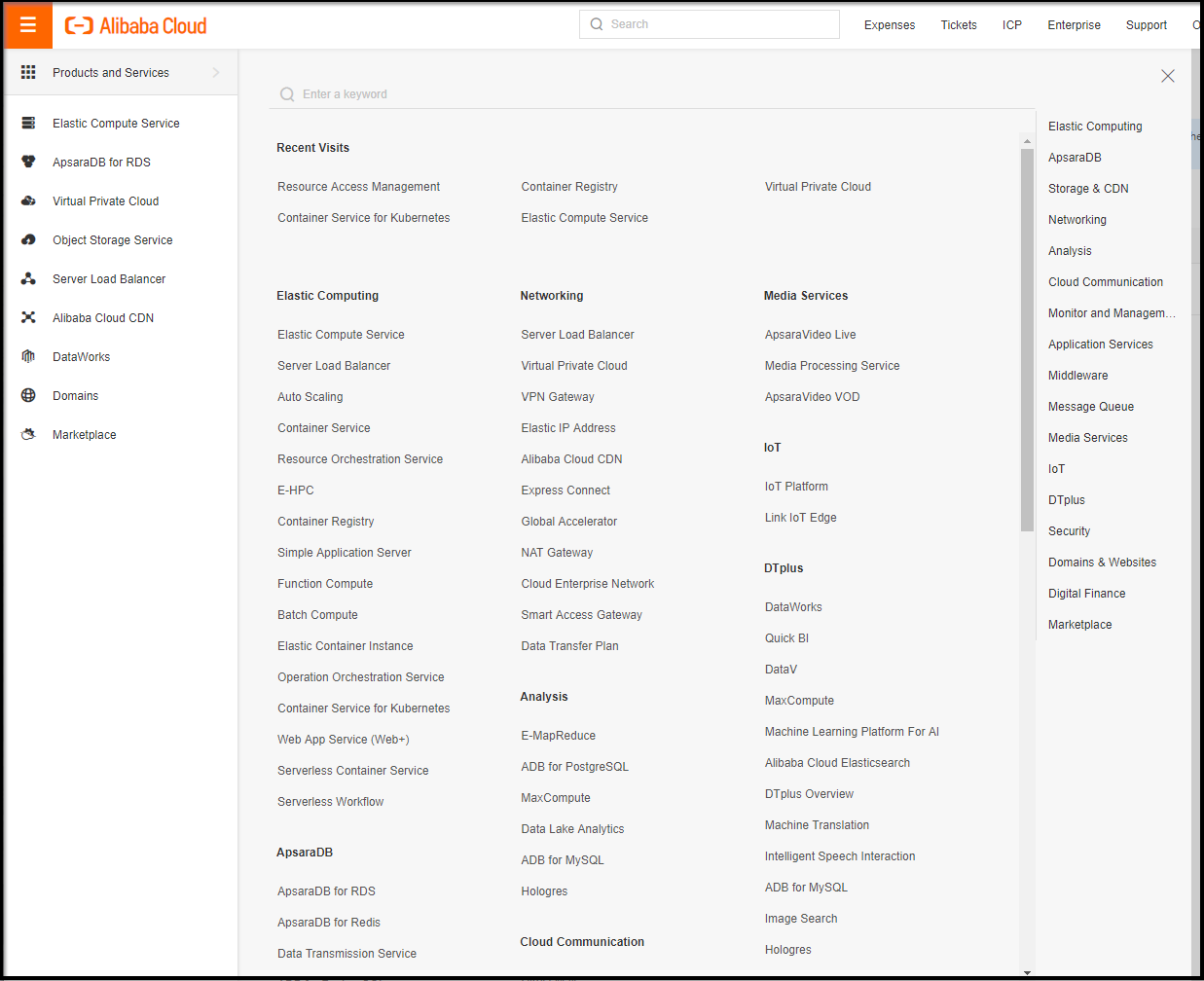
You’ll find a lot of familiar things. Their k8s is setup a lot like AWS EKS. And they have a cloud console just like Azure.
Here are just some of the offerings:
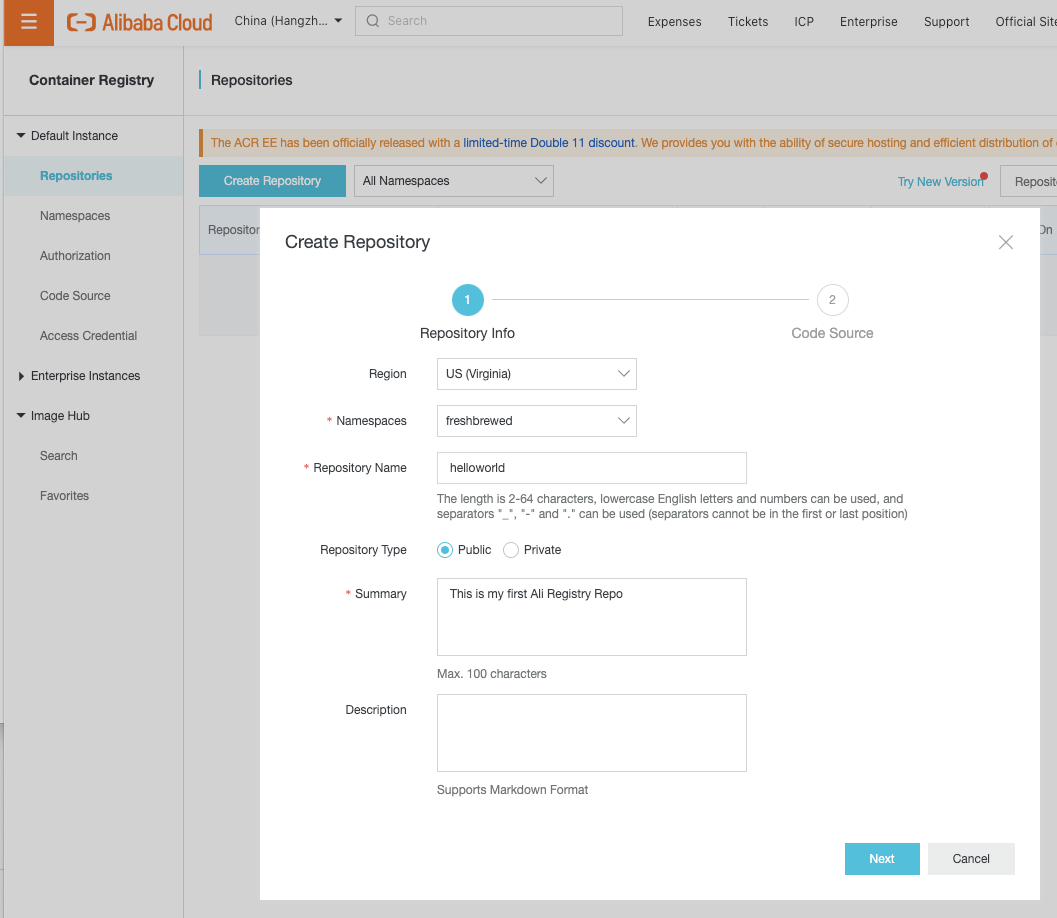
Creating a Container Registry
Go to Container Registries to create a Repository
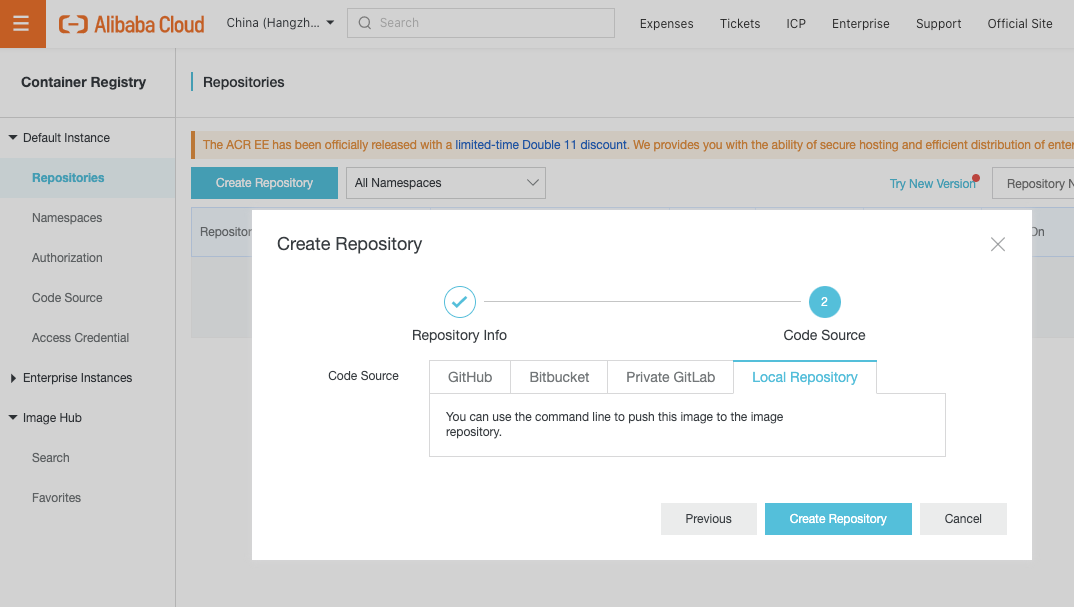
Now we can build from a Git location such as Github and Gitlab.. But i’m just looking to store containers…
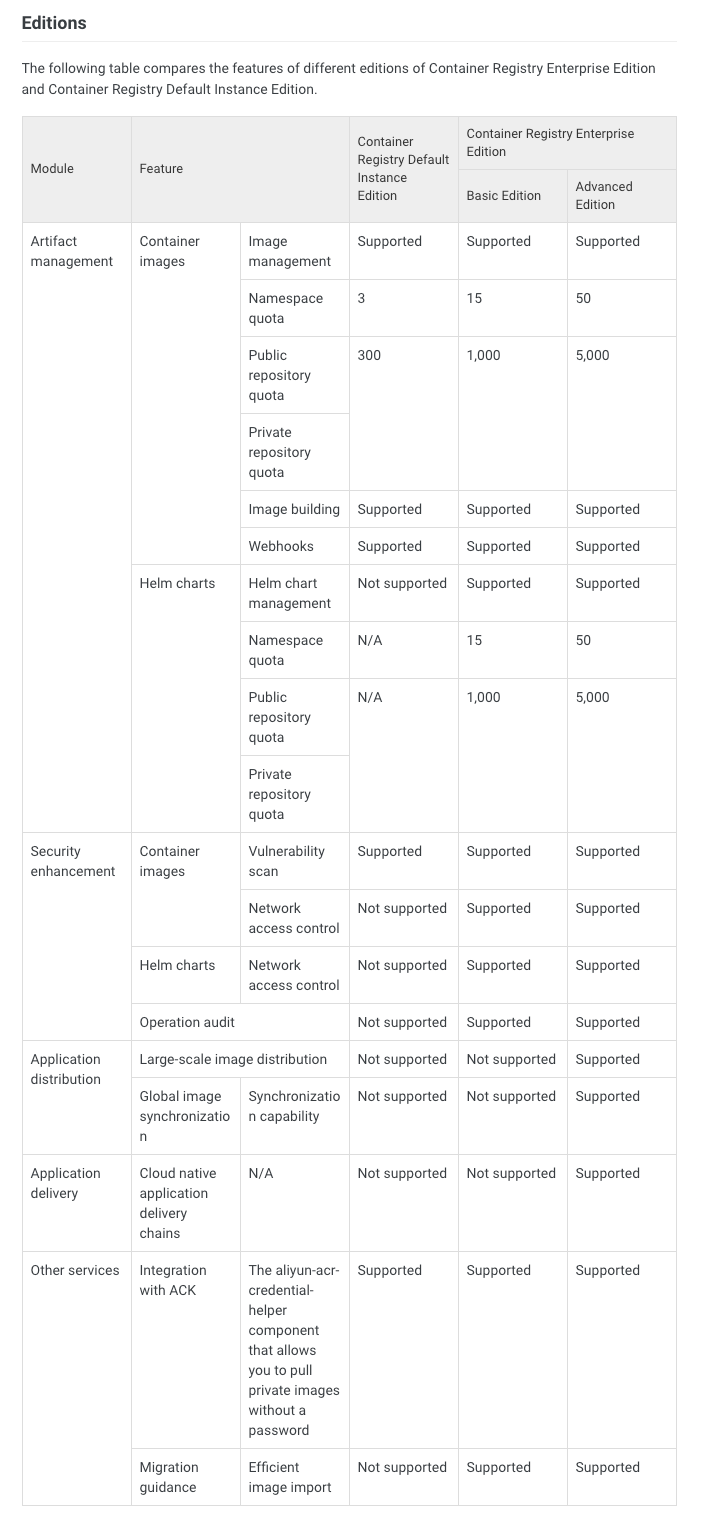
Which this creates, let’s dig into what the “Default Instance Edition” gives us in this table: https://www.alibabacloud.com/help/doc-detail/64340.htm?spm=a3c0i.11159930.4984389550.1.22c17ff9h2zk8K
The pricing is free.. But you have to carefully watch their words. It does indicate this is in public free preview
Container Registry Default Instance Edition is available only for individual developers. Individual developers are allocated a limited free quota during the public preview period. Alibaba Cloud does not make compensation in accordance with the service level agreement (SLA) for Container Registry Default Instance Edition
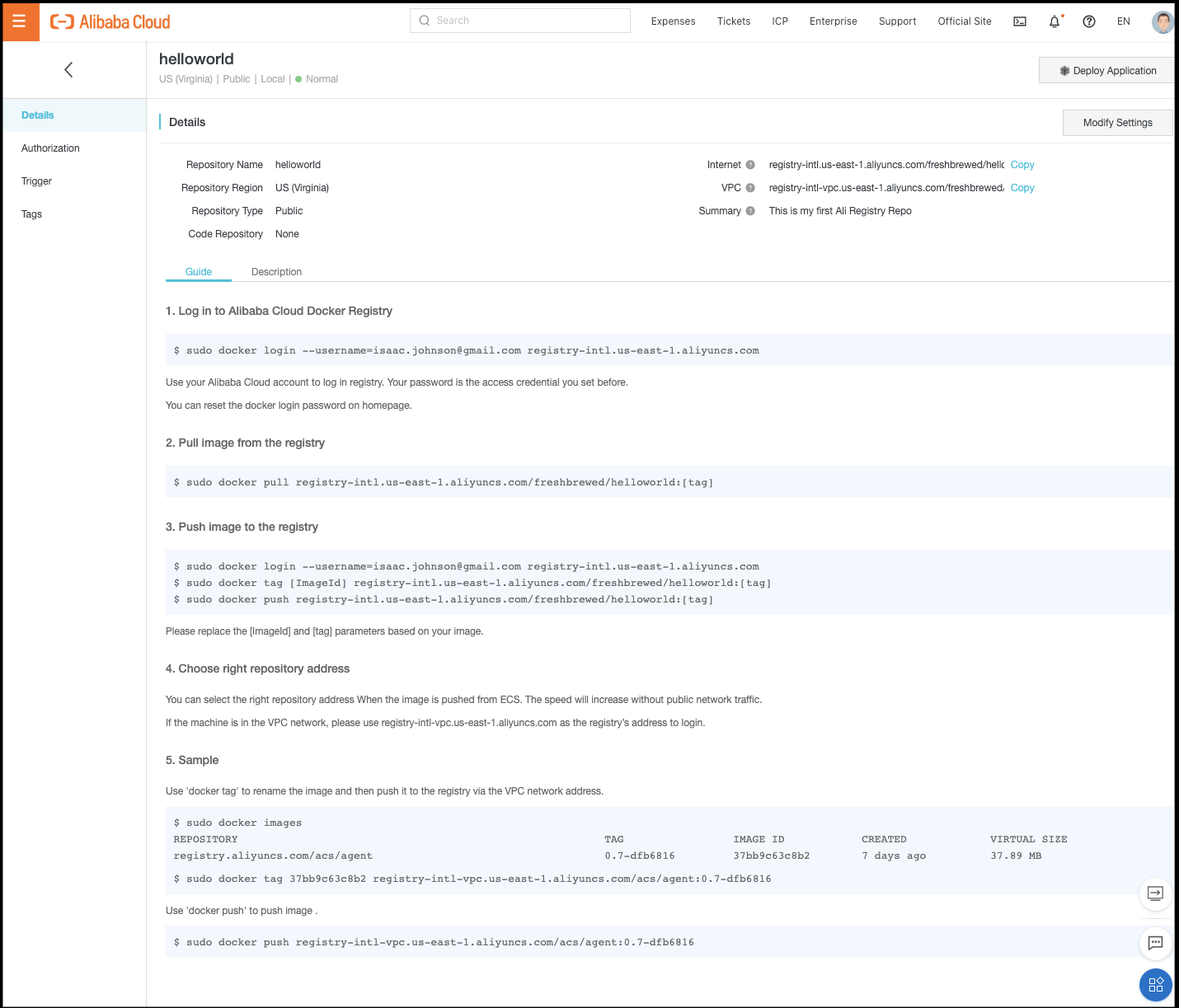
Details of our registry.. If we go to details, we see all the solid info to use: https://cr.console.aliyun.com/repository/us-east-1/freshbrewed/helloworld/details
Now that it’s created, let’s try it out
Using AliCloud Container Registry
During our creation, we created a password (different from the cloud login). Let’s use that with our login
$ docker login --username=isaac.johnson@gmail.com registry-intl.us-east-1.aliyuncs.com
Password:
Login Succeeded
Let’s pull a Hello World image, tag, then push it
$ docker pull hello-world
Using default tag: latest
latest: Pulling from library/hello-world
0e03bdcc26d7: Pull complete
Digest: sha256:e7c70bb24b462baa86c102610182e3efcb12a04854e8c582838d92970a09f323
Status: Downloaded newer image for hello-world:latest
docker.io/library/hello-world:latest
$ docker tag hello-world:latest registry-intl.us-east-1.aliyuncs.com/freshbrewed/helloworld:1
$ docker push registry-intl.us-east-1.aliyuncs.com/freshbrewed/helloworld:1
The push refers to repository [registry-intl.us-east-1.aliyuncs.com/freshbrewed/helloworld]
9c27e219663c: Pushed
1: digest: sha256:90659bf80b44ce6be8234e6ff90a1ac34acbeb826903b02cfa0da11c82cbc042 size: 525
Verification
Let’s see what it looks like in AliCloud.
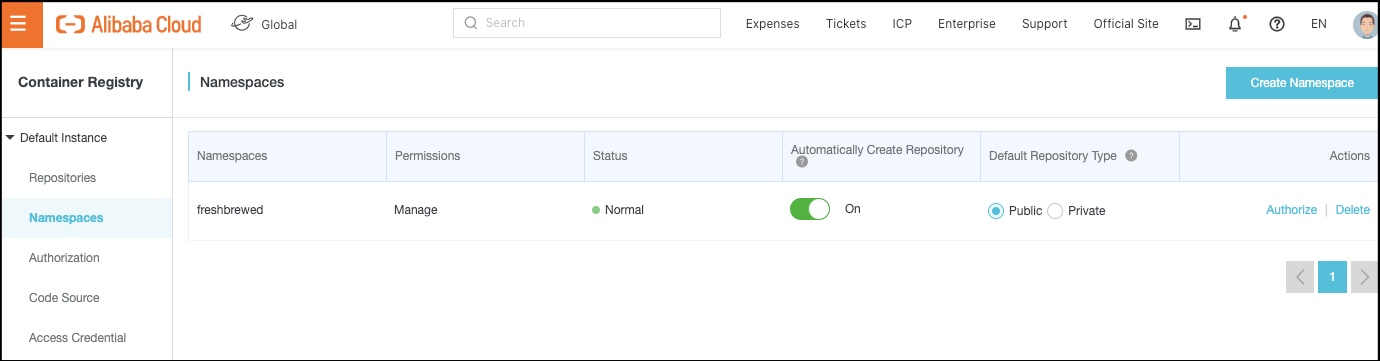
One change I’ll make right now, so that I can use these in a k8s file later, is to change the repo to Public. By Default, they make the actual repository private (even if the namespace is technically Public)
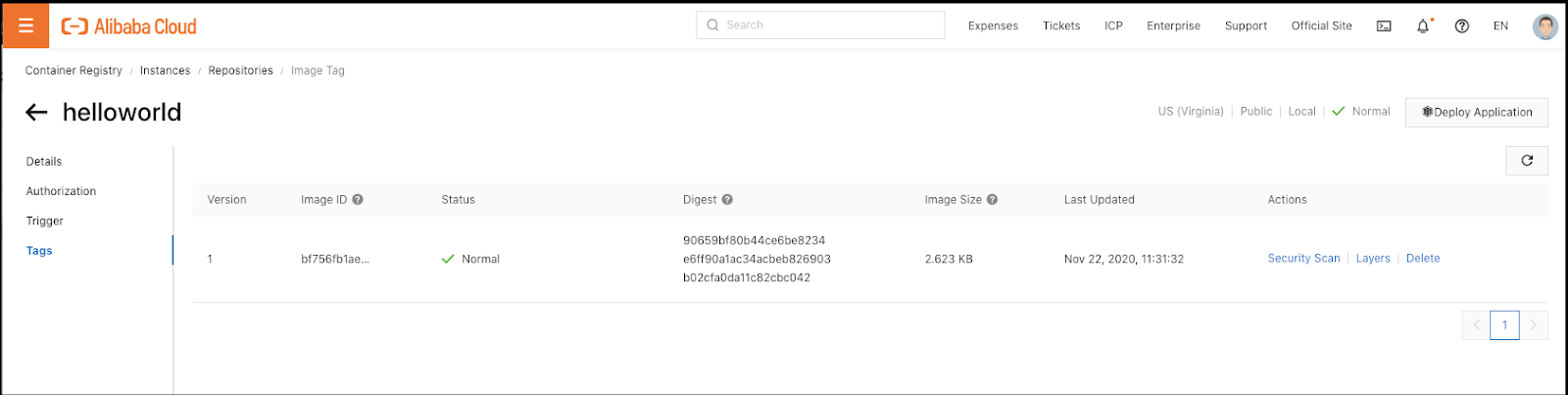
If we go to Tags, we can see more details
Layers show us the various layers in our image:
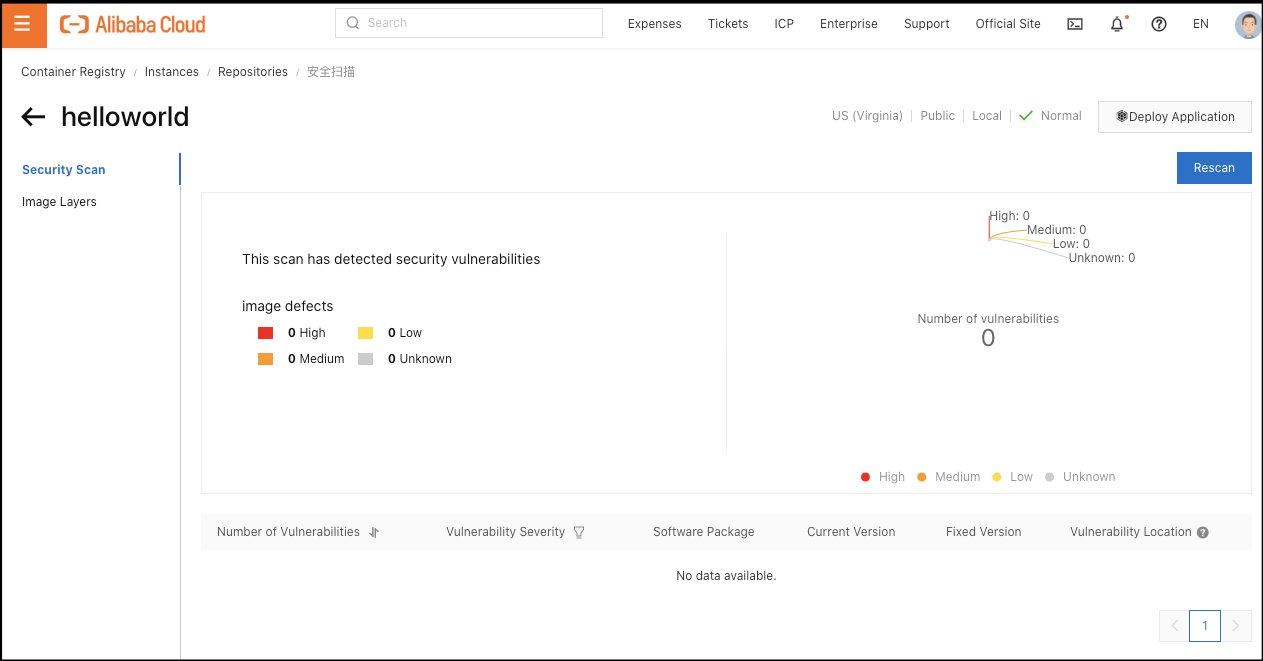
Scan shows us a scan, but you have to “Trigger Scan” to perform a scan
We had an image earlier that had vulnerabilities in IBM cloud.. Let’s pull that down then push to Ali to see if it detects the same CVEs.
Here we will pull the exact image with issues, then tag it and lastly push to AliCloud
$ docker pull us.icr.io/freshbrewedcr/hello@sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6
sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6: Pulling from freshbrewedcr/hello
cbdbe7a5bc2a: Already exists
f2ffd52523c3: Pull complete
48a445fb9d78: Pull complete
7a27e63388b2: Pull complete
a6c7dc586cf8: Pull complete
801108715e2a: Pull complete
ed1cc0031275: Pull complete
1d1ce53598e8: Pull complete
Digest: sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6
Status: Downloaded newer image for us.icr.io/freshbrewedcr/hello@sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6
us.icr.io/freshbrewedcr/hello@sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6
$ docker images | grep hello
us.icr.io/freshbrewedcr/hello <none> 8f16abce8b97 2 days ago 126MB
hello-world latest bf756fb1ae65 10 months ago 13.3kB
$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
us.icr.io/freshbrewedcr/hello <none> 8f16abce8b97 2 days ago 126MB
freshbrewed/webapp 0.2.0 05bd0d1575ab 3 weeks ago 429MB
freshbrewed/webapp 0.2.0-20201029152949 05bd0d1575ab 3 weeks ago 429MB
freshbrewed/webapp latest 05bd0d1575ab 3 weeks ago 429MB
idjk8senv5cr.azurecr.io/freshbrewed/webapp latest 05bd0d1575ab 3 weeks ago 429MB
ijk8senv5cr.azurecr.io/freshbrewed/webapp latest 05bd0d1575ab 3 weeks ago 429MB
freshbrewed/haproxy 1.6.11 66ce07f6e5f6 3 weeks ago 207MB
freshbrewed/haproxy 1.6.11-20201029152918 66ce07f6e5f6 3 weeks ago 207MB
freshbrewed/haproxy latest 66ce07f6e5f6 3 weeks ago 207MB
<none> <none> 2fbb4b4d7f8d 4 weeks ago 106MB
hello-world latest bf756fb1ae65 10 months ago 13.3kB
us.icr.io/freshbrewedcr/hw_repo 2 bf756fb1ae65 10 months ago 13.3kB
$ docker tag 8f16abce8b97 registry-intl.us-east-1.aliyuncs.com/freshbrewed/hello:1
$ docker push registry-intl.us-east-1.aliyuncs.com/freshbrewed/hello:1
The push refers to repository [registry-intl.us-east-1.aliyuncs.com/freshbrewed/hello]
7c541fb5f502: Pushed
34db062e62b1: Pushed
b849b293e74f: Pushed
1187fe3a30a8: Pushed
91f164a34974: Pushed
6eff1efe8a1e: Pushed
969acb16219d: Pushed
3e207b409db3: Pushed
1: digest: sha256:2030c86a2ada1847773a58525911e9bced002c9b3440491a2d8c6d780d9911f6 size: 1992
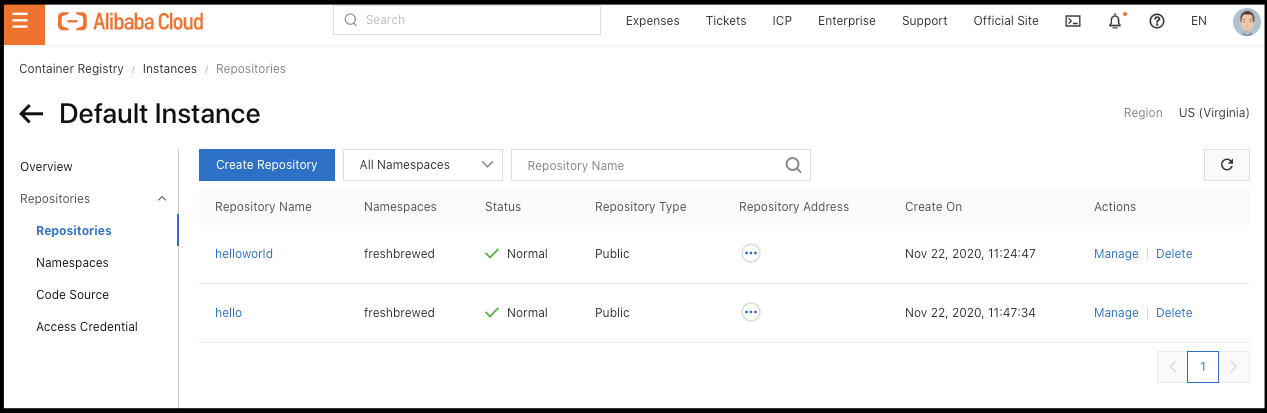
We can now see Hello was added to our Repositories:
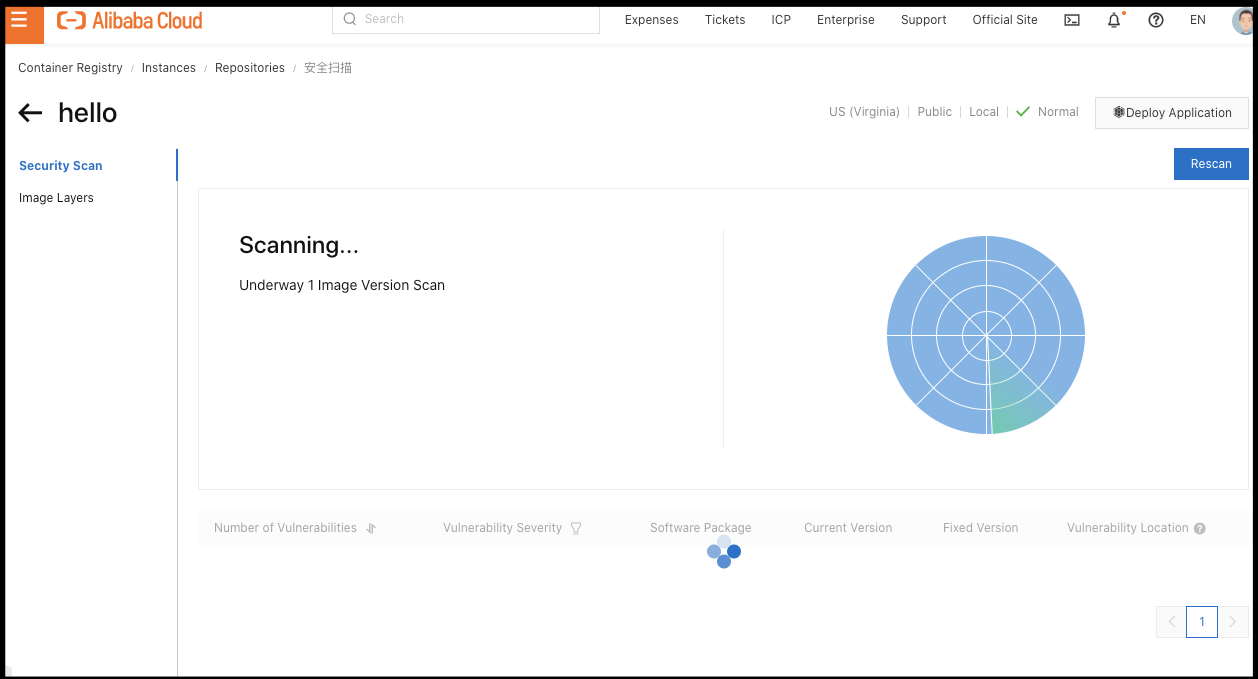
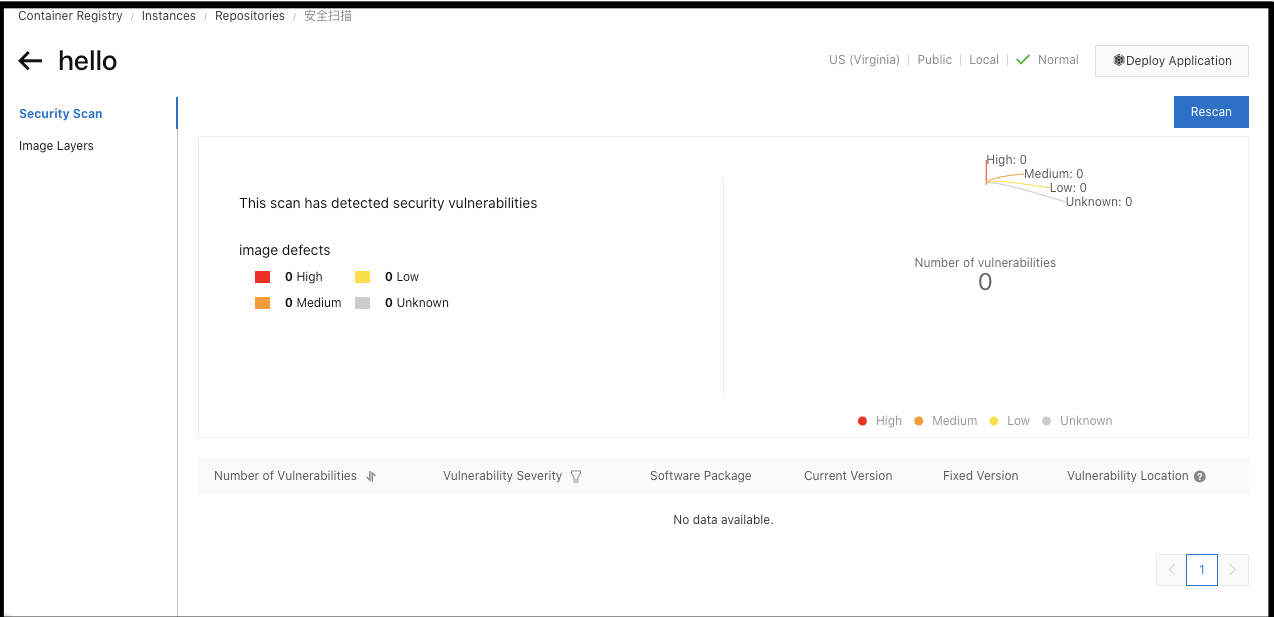
Let’s go to tags and click security scan
However, it did not detect the CVE that IBM Cloud had:
This is supposedly all in the free tier which is great.. The question becomes will it cost us later.
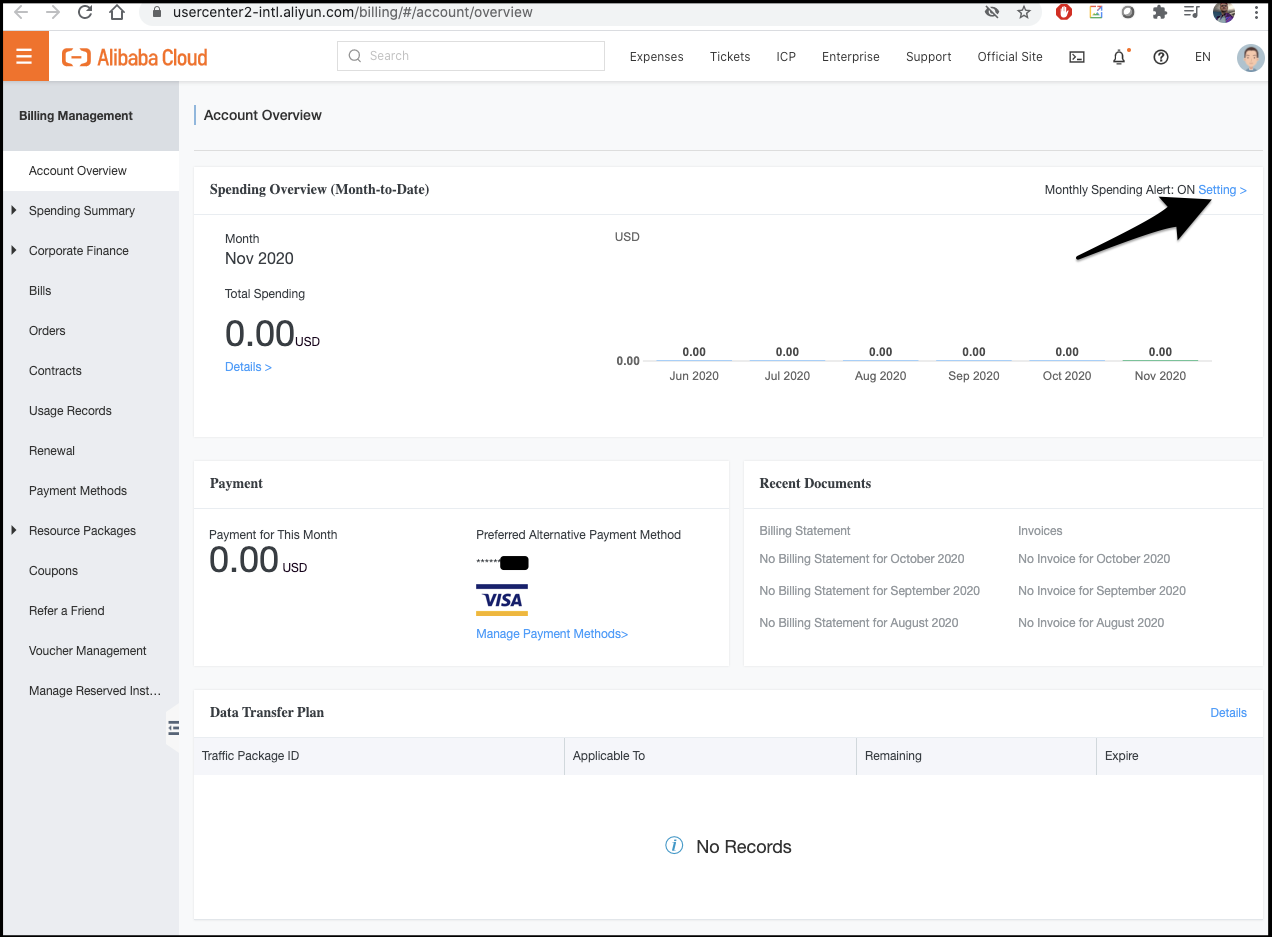
Luckily, AliCloud lets us set a “spending alert” so we can get an email notification if we cross a threshold.
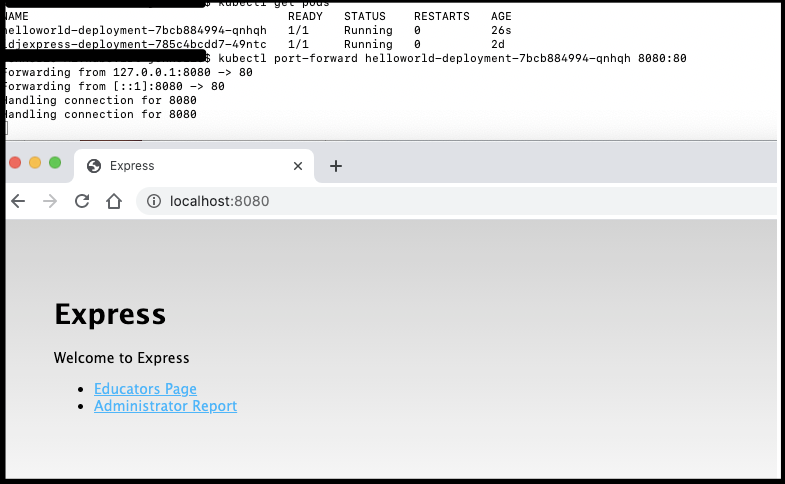
Testing in K8s…
Since we set the repository as public, it should let us useit without specifying pull credentials.
Create a deployment.yaml
$ cat deployment.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: helloworld-deployment
labels:
app: helloworld
spec:
replicas: 1
selector:
matchLabels:
app: helloworld
template:
metadata:
labels:
app: helloworld
spec:
containers:
- name: helloworld
image: registry-intl.us-east-1.aliyuncs.com/freshbrewed/hello:1
ports:
- containerPort: 80
Deploy and check logs:
$ kubectl apply -f deployment.yaml
deployment.apps/helloworld-deployment created
$ kubectl get pods
NAME READY STATUS RESTARTS AGE
helloworld-deployment-7bcb884994-qnhqh 0/1 ContainerCreating 0 10s
idjexpress-deployment-785c4bcdd7-49ntc 1/1 Running 0 2d
$ kubectl logs helloworld-deployment-7bcb884994-qnhqh
> myapp@0.0.0 start /app
> node ./bin/www
Port-forward to test
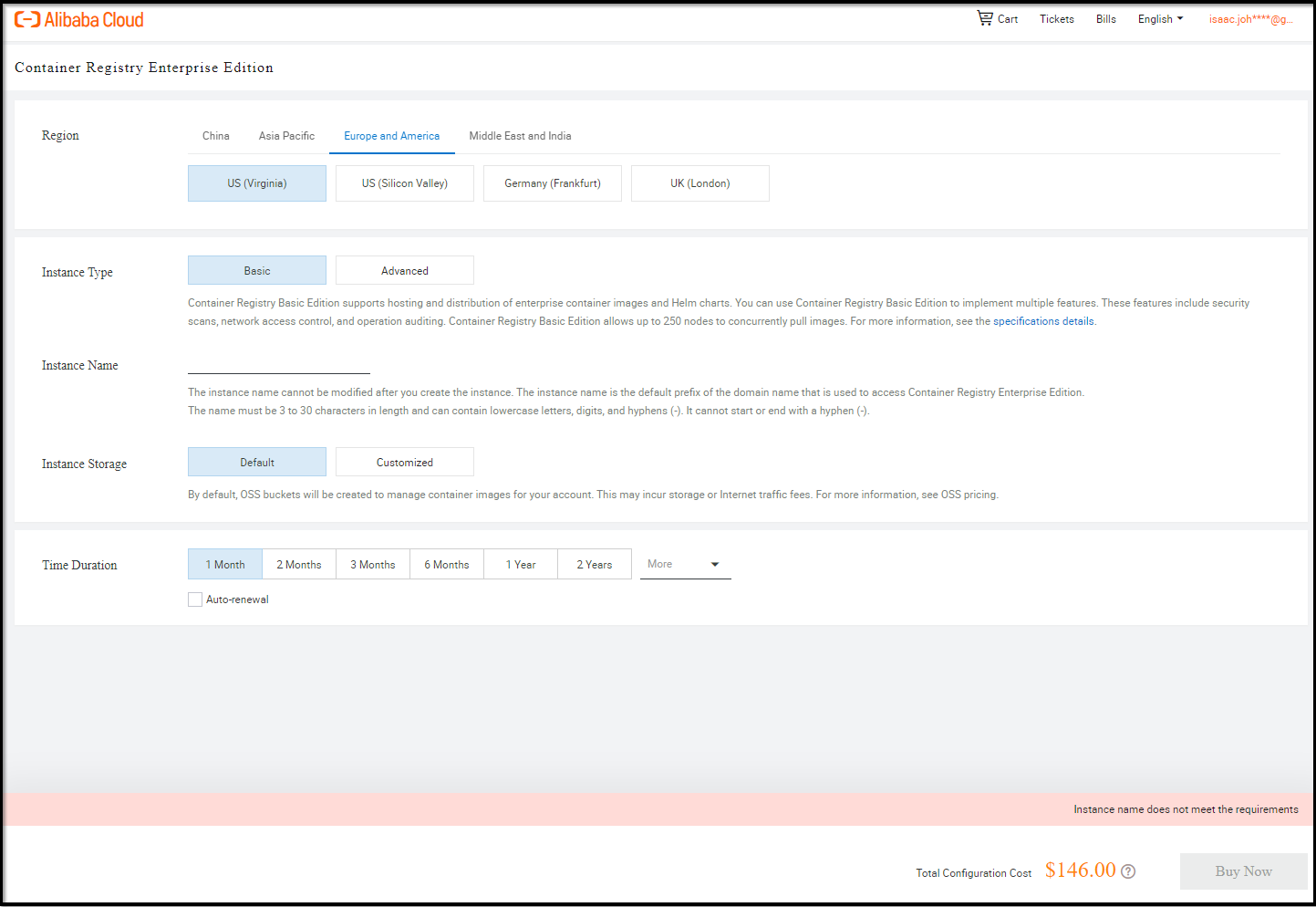
Enterprise Instance
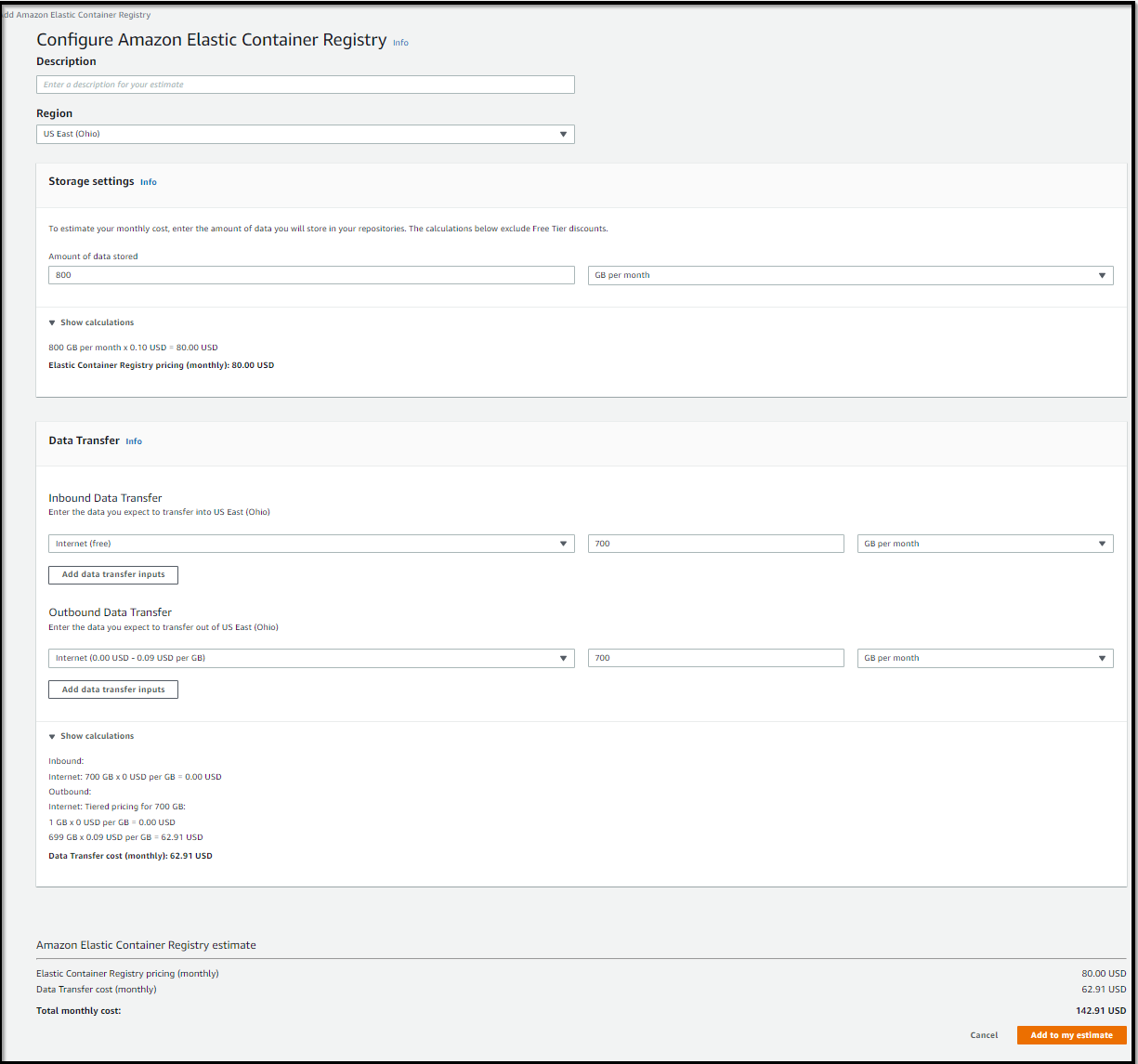
I’m not going to signup for the Container Registry Enterprise Edition, but we can see a price to compare to other services.
The most basic would run us $146
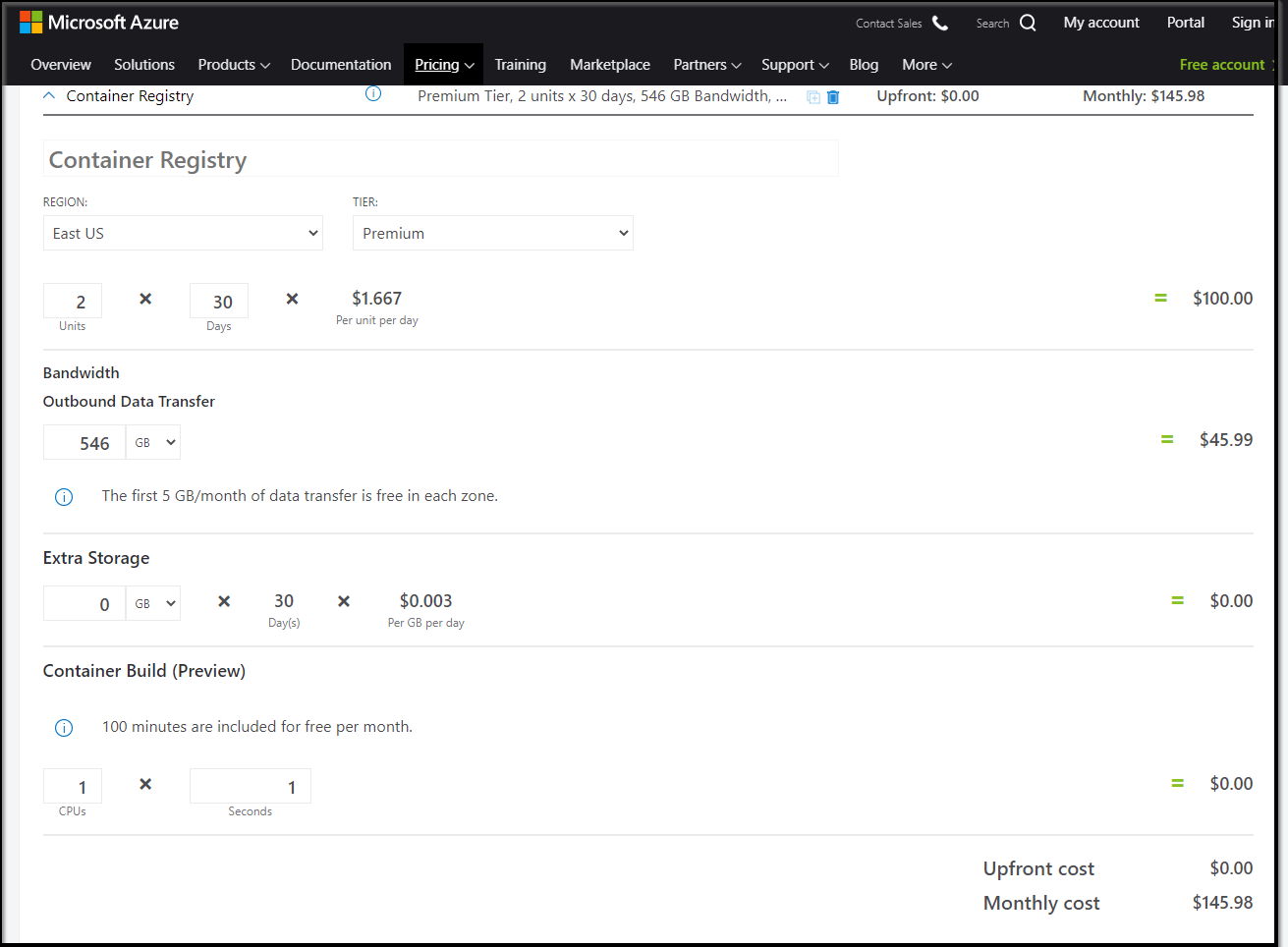
For Azure, that would get us two instances for geo-replication with about 546Gb of outbound transfer included
Which is in the ballpark for a singe ECR space but with a bit more transfer
Summary
AliCloud is an interesting provider. It’s a Chinese company found in 2009 under the AliBaba Group. It has 21 regions and 63 availability zones making a real global player. But is definitely an Asia-first product. Some pages (like their message service) load in Japanese for me and I needed to use google translate. The English wording on some alerts requires a few reads to figure out.
And I still cannot figure out the real limits of their ?free Container Registry. I can tell you, anecdotally, that it’s fast. The push and pulls and launching of that container into a few different Kubernetes clusters was surprisingly quick.
I plan to try this for a bit and see if the costs take off. For now, this is the best free offering I’ve found.