Published: Apr 6, 2020 by Isaac Johnson
Azure Arc is a preview feature for Azure that will let you manage in Azure resources outside of Azure. So far they’ve discussed Arc for databases, servers and Kubernetes. I was recently given access to the Preview of Arc for servers. Let’s check out what’s there and what it can do at present.
Adding an Arc Server
We can start by adding a Linode instance into our Resource Group. Start in Azure with the Create Wizard.
Let’s add Azure Arc for servers:
We will need to pick our Subscription and Resource Group as well as OS:
When we click create, we can see the Install script:
Next, I’ll hop over to Linode and create a new nano node to test.
We can ssh in and run the script:
You’ll need to login for that last line:
root@localhost:~# azcmagent connect --resource-group "idjaks04rg" --tenant-id "xxxxx-xxxxxx-xxxxxxx-xxxxxxx" --location "westus2" --subscription-id "xxxxxxxx-xxxxxxxx-xxxxxxx-xxxxxxx"
level=info msg="Onboarding Machine. It usually takes a few minutes to complete. Sometimes it may take longer depending on network and server load status."
To sign in, use a web browser to open the page https://microsoft.com/devicelogin and enter the code FFW3RGW9H to authenticate.
level=info msg="Successfully Onboarded Resource to Azure" VM Id=cb9b5edf-a16a-49c6-acbf-a08127bf6bef
root@localhost:~#
One issue I did see is that the “hostname” is used for machine name. So after adding we see this listed as “localhost” in the Azure Portal. The other entry was from a CentOS host i also added.
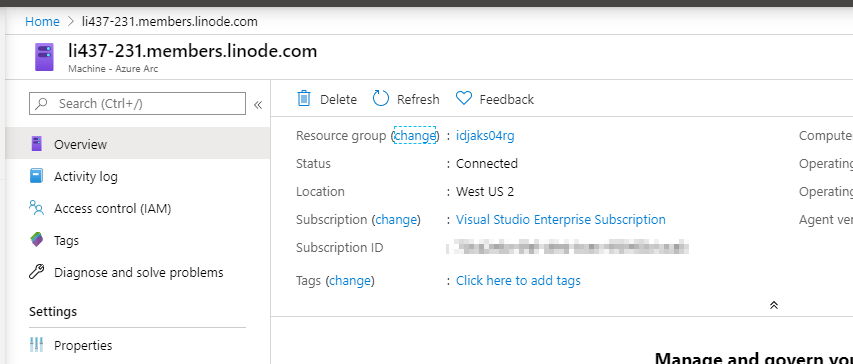
As you can see, I have Azure Arc loaded with my Linode server. It’s been there about a week.
From Linode:
And from Azure Portal:
By default, we can’t do much without adding Log Analytics:
What happens when we power off?
Now that it’s offline:
At first, i still saw it connected in Azure Portal:
However after a few minutes, it noted that it had gone offline:
Even with Azure Log analytics on, we really can only see if it’s powered on or off.
Arc Policies
Let’s add a policy for Azure Log Analytics.
We can check on policies, like Azure Log Analytics for Linux, we can set a policy that shows if it’s missing and (supposedly) install it:
But i didn’t install it. We could then install it and validate (https://docs.microsoft.com/en-us/azure/azure-monitor/platform/agent-linux#install-the-agent-using-wrapper-script) if we desired.
Windows
What about windows? We will use AWS to test this one (since Linode, by it’s name, just does Linux).
First, let’s create a key-pair for logging in later: https://us-east-2.console.aws.amazon.com/ec2/v2/home?region=us-east-2#KeyPairs:
We’ll create a PEM key pair.
I want to launch a set of EC2 Windows servers quickly. I found a decent quite start for creating an HA cluster of RDS Bastion hosts here: https://docs.aws.amazon.com/quickstart/latest/rd-gateway/welcome.html
Click “Launch Quick Start”
In the template, you’ll want to use your CIDR block and the Key Pair we created.
If that confuses you, just google “what is my IP”, drop the last digit and slap a “0/24” there. That covers from .1 to .255 which for me, would likely cover my outgoing connections from Xfinity.
Lower, we’ll need a password and domain name. I don’t think it needs a corresponding R53. I’ll assume you could put anything you want there.
My Parameters look something like this:
Once we accept the IAM Creation notification and click create, we should see Cloudformation kick in to create our stack:
Once done:
We can use StackAdmin (the admin account we specified in the template) to login:
Now, back in our Azure Portal, let’s create a new Arc server, this time set it to be windows:
In our Remote Desktop session, launch and admin powershell. I found the clipboard wasn’t pasting, so i saved the contents into a notepad and ran that:
Going back to our RG, we should see the new machine added:
But again, our Logs are not populated just by adding the Agent. So let’s create a Log Analytics Workspace in our RG:
I’ll then go to the workspace to download the client and see the settings;
We’ll use the workspace, but not Systems Operations Center for this demo.
If we look up the monitoring agent in the control panel, we can see it’s alive in the second tab:
We can use the Heartbeat check to see if it’s alive: Heartbeat| where TimeGenerated > ago(30m)
_ However _, I can do the same in the root workspace as well:
So what is this buying us? I like the idea of compliance checks…
For instance, we set one to install the log agent, if absent, on linux. However, we can go back and see there are still no logs (after a couple days):
So either it didn’t actually install the agent and the check is in err or it installed it but didn’t configure or start it, equally useless to me.
Cleanup
AWS
Let’s go to Stack in CloudFormation and delete the root stack:
In Linode, you’ll want to delete your instances. I learned the hard way with DigitalOcean, you still get billed for powered off machines (DO charges full price too):
In Azure, you can either delete the whole RG or just the instances in it:
In my case, I still want to experiment more with the Ubuntu host.
Summary
Azure Arc is interesting. I think there could be potential there to do some interesting things. I have to assume it’s either the earliness of the preview or settings on my end that prevented me from doing anything useful with it. For now, i’ll just say it needs some time to bake before it’s worth using for anything other than monitoring whether machines are powered on.


